Support Questions
- Cloudera Community
- Support
- Support Questions
- Re: NIFI-1.16.0 insufficient permissions while per...
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
NIFI-1.16.0 insufficient permissions while performing any action
- Labels:
-
Apache NiFi
Created on
06-07-2022
10:05 AM
- last edited on
06-07-2022
11:04 AM
by
DianaTorres
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
HI Team,
System Env Details: I am trying setup NIFI on AWS
3 node cluster
NIFI version: 1.16.0
authorisers.xml :
<userGroupProvider>
<identifier>file-user-group-provider</identifier>
<class>org.apache.nifi.authorization.FileUserGroupProvider</class>
<property name="Users File">./conf/users.xml</property>
<property name="Legacy Authorized Users File"></property>
<property name="Initial User Identity 1">xxx@xxx.com</property>
<property name="Initial User Identity 2">C=US, ST=xxx, O=xxx, OU=xxxx, CN=%%cn_user_identity_1%%</property>
<property name="Initial User Identity 3">C=US, ST=xxx, O=xxx, OU=xxxx, CN=%%cn_user_identity_2%%</property>
<property name="Initial User Identity 4">C=US, ST=xxxxx, O=xxxx, OU=xxxx, CN=%%cn_user_identity_3%%</property>
</userGroupProvider>
<accessPolicyProvider>
<identifier>file-access-policy-provider</identifier>
<class>org.apache.nifi.authorization.FileAccessPolicyProvider</class>
<property name="User Group Provider">file-user-group-provider</property>
<property name="Authorizations File">./conf/authorizations.xml</property>
<property name="Initial Admin Identity">xxxx@xxxxx.com</property>
<property name="Legacy Authorized Users File"></property>
<property name="Node Identity 1">C=US, ST=xxx, O=xxx, OU=xxx, CN=%%cn_node_identity_1%%</property>
<property name="Node Identity 2">C=US, ST=xxx, O=xx, OU=xxx, CN=%%cn_node_identity_2%%</property>
<property name="Node Identity 3">C=US, ST=xxxx, O=xxxxx, OU=xxxx, CN=%%cn_node_identity_3%%</property>
<property name="Node Group"></property>
</accessPolicyProvider>
nifi.properties
# Core Properties #
nifi.flow.configuration.file=./conf/flow.xml.gz
nifi.flow.configuration.json.file=./conf/flow.json.gz
nifi.flow.configuration.archive.enabled=true
nifi.flow.configuration.archive.dir=./conf/archive/
nifi.flow.configuration.archive.max.time=30 days
nifi.flow.configuration.archive.max.storage=500 MB
nifi.flow.configuration.archive.max.count=
nifi.flowcontroller.autoResumeState=true
nifi.flowcontroller.graceful.shutdown.period=10 sec
nifi.flowservice.writedelay.interval=500 ms
nifi.administrative.yield.duration=30 sec
# If a component has no work to do (is "bored"), how long should we wait before checking again for work?
nifi.bored.yield.duration=10 millis
nifi.queue.backpressure.count=10000
nifi.queue.backpressure.size=1 GB
nifi.authorizer.configuration.file=./conf/authorizers.xml
nifi.login.identity.provider.configuration.file=./conf/login-identity-providers.xml
nifi.templates.directory=./conf/templates
nifi.ui.banner.text=
nifi.ui.autorefresh.interval=30 sec
nifi.nar.library.directory=./lib
nifi.nar.library.autoload.directory=./extensions
nifi.nar.working.directory=./work/nar/
nifi.documentation.working.directory=./work/docs/components
####################
# State Management #
####################
nifi.state.management.configuration.file=./conf/state-management.xml
# The ID of the local state provider
nifi.state.management.provider.local=local-provider
# The ID of the cluster-wide state provider. This will be ignored if NiFi is not clustered but must be populated if running in a cluster.
nifi.state.management.provider.cluster=zk-provider
# Specifies whether or not this instance of NiFi should run an embedded ZooKeeper server
nifi.state.management.embedded.zookeeper.start=false
# Properties file that provides the ZooKeeper properties to use if <nifi.state.management.embedded.zookeeper.start> is set to true
nifi.state.management.embedded.zookeeper.properties=./conf/zookeeper.properties
# H2 Settings
nifi.database.directory=%%base_path%%/database_repository
nifi.h2.url.append=;LOCK_TIMEOUT=25000;WRITE_DELAY=0;AUTO_SERVER=FALSE
# Repository Encryption properties override individual repository implementation properties
nifi.repository.encryption.protocol.version=
nifi.repository.encryption.key.id=
nifi.repository.encryption.key.provider=
nifi.repository.encryption.key.provider.keystore.location=
nifi.repository.encryption.key.provider.keystore.password=
# FlowFile Repository
nifi.flowfile.repository.implementation=org.apache.nifi.controller.repository.WriteAheadFlowFileRepository
nifi.flowfile.repository.wal.implementation=org.apache.nifi.wali.SequentialAccessWriteAheadLog
nifi.flowfile.repository.directory=%%base_path%%/flowfile_repository
nifi.flowfile.repository.checkpoint.interval=2 mins
nifi.flowfile.repository.always.sync=false
nifi.flowfile.repository.retain.orphaned.flowfiles=true
nifi.swap.manager.implementation=org.apache.nifi.controller.FileSystemSwapManager
nifi.queue.swap.threshold=20000
# Content Repository
nifi.content.repository.implementation=org.apache.nifi.controller.repository.FileSystemRepository
nifi.content.claim.max.appendable.size=1 MB
nifi.content.repository.directory.default=%%base_path%%/content_repository
nifi.content.repository.archive.max.retention.period=12 hours
nifi.content.repository.archive.max.usage.percentage=50%
nifi.content.repository.archive.enabled=true
nifi.content.repository.always.sync=false
nifi.content.viewer.url=../nifi-content-viewer/
# Provenance Repository Properties
nifi.provenance.repository.implementation=org.apache.nifi.provenance.WriteAheadProvenanceRepository
# Persistent Provenance Repository Properties
nifi.provenance.repository.directory.default=%%base_path%%/provenance_repository
nifi.provenance.repository.max.storage.time=24 hours
nifi.provenance.repository.max.storage.size=1 GB
nifi.provenance.repository.rollover.time=30 secs
nifi.provenance.repository.rollover.size=100 MB
nifi.provenance.repository.query.threads=2
nifi.provenance.repository.index.threads=2
nifi.provenance.repository.compress.on.rollover=true
nifi.provenance.repository.always.sync=false
# Comma-separated list of fields. Fields that are not indexed will not be searchable. Valid fields are:
# EventType, FlowFileUUID, Filename, TransitURI, ProcessorID, AlternateIdentifierURI, Relationship, Details
nifi.provenance.repository.indexed.fields=EventType, FlowFileUUID, Filename, ProcessorID, Relationship
# FlowFile Attributes that should be indexed and made searchable. Some examples to consider are filename, uuid, mime.type
nifi.provenance.repository.indexed.attributes=
# Large values for the shard size will result in more Java heap usage when searching the Provenance Repository
# but should provide better performance
nifi.provenance.repository.index.shard.size=500 MB
# Indicates the maximum length that a FlowFile attribute can be when retrieving a Provenance Event from
# the repository. If the length of any attribute exceeds this value, it will be truncated when the event is retrieved.
nifi.provenance.repository.max.attribute.length=65536
nifi.provenance.repository.concurrent.merge.threads=2
# Volatile Provenance Respository Properties
nifi.provenance.repository.buffer.size=100000
# Component and Node Status History Repository
nifi.components.status.repository.implementation=org.apache.nifi.controller.status.history.VolatileComponentStatusRepository
# Volatile Status History Repository Properties
nifi.components.status.repository.buffer.size=1440
nifi.components.status.snapshot.frequency=1 min
# QuestDB Status History Repository Properties
nifi.status.repository.questdb.persist.node.days=14
nifi.status.repository.questdb.persist.component.days=3
nifi.status.repository.questdb.persist.location=%%base_path%%/status_repository
# Site to Site properties
nifi.remote.input.host=%%host_name%%
nifi.remote.input.secure=true
nifi.remote.input.socket.port=10443
nifi.remote.input.http.enabled=true
nifi.remote.input.http.transaction.ttl=30 sec
nifi.remote.contents.cache.expiration=30 secs
# web properties #
#############################################
# For security, NiFi will present the UI on 127.0.0.1 and only be accessible through this loopback interface.
# Be aware that changing these properties may affect how your instance can be accessed without any restriction.
# We recommend configuring HTTPS instead. The administrators guide provides instructions on how to do this.
nifi.web.http.host=
nifi.web.http.port=
nifi.web.http.network.interface.default=
#############################################
nifi.web.https.host=%%host_name%%
nifi.web.https.port=8086
nifi.web.https.network.interface.default=
nifi.web.jetty.working.directory=./work/jetty
nifi.web.jetty.threads=200
nifi.web.max.header.size=16 KB
nifi.web.proxy.context.path=
nifi.web.proxy.host=%%proxy_hostname%%:443
nifi.web.max.content.size=
nifi.web.max.requests.per.second=30000
nifi.web.max.access.token.requests.per.second=25
nifi.web.request.timeout=60 secs
nifi.web.request.ip.whitelist=
nifi.web.should.send.server.version=true
nifi.web.request.log.format=%{client}a - %u %t "%r" %s %O "%{Referer}i" "%{User-Agent}i"
# Include or Exclude TLS Cipher Suites for HTTPS
nifi.web.https.ciphersuites.include=
nifi.web.https.ciphersuites.exclude=
# security properties #
nifi.sensitive.props.key=***************
nifi.sensitive.props.key.protected=
nifi.sensitive.props.algorithm=NIFI_PBKDF2_AES_GCM_256
nifi.sensitive.props.additional.keys=
nifi.security.autoreload.enabled=false
nifi.security.autoreload.interval=10 secs
nifi.security.keystore=%%base_path%%/certs/SSL/%%host_name%%.keystore
nifi.security.keystoreType=jks
nifi.security.keystorePasswd=**********
nifi.security.keyPasswd=*********
nifi.security.truststore=%%base_path%%/certs/SSL/truststore.jks
nifi.security.truststoreType=jks
nifi.security.truststorePasswd=***********
nifi.security.user.authorizer=managed-authorizer
nifi.security.allow.anonymous.authentication=false
nifi.security.user.login.identity.provider=
nifi.security.user.jws.key.rotation.period=
nifi.security.ocsp.responder.url=
nifi.security.ocsp.responder.certificate=
# OpenId Connect SSO Properties #
nifi.security.user.oidc.discovery.url=
nifi.security.user.oidc.connect.timeout=5 secs
nifi.security.user.oidc.read.timeout=5 secs
nifi.security.user.oidc.client.id=
nifi.security.user.oidc.client.secret=
nifi.security.user.oidc.preferred.jwsalgorithm=
nifi.security.user.oidc.additional.scopes=
nifi.security.user.oidc.claim.identifying.user=
nifi.security.user.oidc.fallback.claims.identifying.user=
nifi.security.user.oidc.truststore.strategy=JDK
# Apache Knox SSO Properties #
nifi.security.user.knox.url=
nifi.security.user.knox.publicKey=
nifi.security.user.knox.cookieName=hadoop-jwt
nifi.security.user.knox.audiences=
# SAML Properties #
nifi.security.user.saml.idp.metadata.url=file://%%base_path%%/certs/IDMS/idms-xxxxx.xml
nifi.security.user.saml.sp.entity.id=xxxxxxx
nifi.security.user.saml.identity.attribute.name=email
nifi.security.user.saml.group.attribute.name=
nifi.security.user.saml.metadata.signing.enabled=false
nifi.security.user.saml.request.signing.enabled=false
nifi.security.user.saml.want.assertions.signed=true
nifi.security.user.saml.signature.algorithm=http://www.w3.org/2001/04/xmldsig-more#rsa-sha256
nifi.security.user.saml.signature.digest.algorithm=http://www.w3.org/2001/04/xmlenc#sha256
nifi.security.user.saml.message.logging.enabled=true
nifi.security.user.saml.authentication.expiration=8 hours
nifi.security.user.saml.single.logout.enabled=false
nifi.security.user.saml.http.client.truststore.strategy=JDK
nifi.security.user.saml.http.client.connect.timeout=30 secs
nifi.security.user.saml.http.client.read.timeout=30 secs
# Identity Mapping Properties #
# These properties allow normalizing user identities such that identities coming from different identity providers
# (certificates, LDAP, Kerberos) can be treated the same internally in NiFi. The following example demonstrates normalizing
# DNs from certificates and principals from Kerberos into a common identity string:
#
# nifi.security.identity.mapping.pattern.dn=^CN=(.*?), OU=(.*?), O=(.*?), L=(.*?), ST=(.*?), C=(.*?)$
# nifi.security.identity.mapping.value.dn=$1@$2
# nifi.security.identity.mapping.transform.dn=NONE
# nifi.security.identity.mapping.pattern.kerb=^(.*?)/instance@(.*?)$
# nifi.security.identity.mapping.value.kerb=$1@$2
# nifi.security.identity.mapping.transform.kerb=UPPER
# Group Mapping Properties #
# These properties allow normalizing group names coming from external sources like LDAP. The following example
# lowercases any group name.
#
# nifi.security.group.mapping.pattern.anygroup=^(.*)$
# nifi.security.group.mapping.value.anygroup=$1
# nifi.security.group.mapping.transform.anygroup=LOWER
# Listener Bootstrap properties #
# This property defines the port used to listen for communications from NiFi Bootstrap. If this property
# is missing, empty, or 0, a random ephemeral port is used.
nifi.listener.bootstrap.port=0
# cluster common properties (all nodes must have same values) #
nifi.cluster.protocol.heartbeat.interval=5 sec
nifi.cluster.protocol.heartbeat.missable.max=8
nifi.cluster.protocol.is.secure=true
# cluster node properties (only configure for cluster nodes) #
nifi.cluster.is.node=true
nifi.cluster.node.address=%%host_name%%
nifi.cluster.node.protocol.port=11443
nifi.cluster.node.protocol.max.threads=50
nifi.cluster.node.event.history.size=25
nifi.cluster.node.connection.timeout=10 sec
nifi.cluster.node.read.timeout=10 sec
nifi.cluster.node.max.concurrent.requests=100
nifi.cluster.firewall.file=
nifi.cluster.flow.election.max.wait.time=1 mins
nifi.cluster.flow.election.max.candidates=
# cluster load balancing properties #
nifi.cluster.load.balance.host=
nifi.cluster.load.balance.port=6342
nifi.cluster.load.balance.connections.per.node=4
nifi.cluster.load.balance.max.thread.count=8
nifi.cluster.load.balance.comms.timeout=30 sec
# zookeeper properties, used for cluster management #
nifi.zookeeper.connect.string=%%zookeeper_connection_strings%%
nifi.zookeeper.connect.timeout=10 secs
nifi.zookeeper.session.timeout=10 secs
nifi.zookeeper.root.node=%%base_path%%/nifi
nifi.zookeeper.client.secure=true
nifi.zookeeper.security.keystore=
nifi.zookeeper.security.keystoreType=
nifi.zookeeper.security.keystorePasswd=
nifi.zookeeper.security.truststore=
nifi.zookeeper.security.truststoreType=
nifi.zookeeper.security.truststorePasswd=
nifi.zookeeper.jute.maxbuffer=
# Zookeeper properties for the authentication scheme used when creating acls on znodes used for cluster management
# Values supported for nifi.zookeeper.auth.type are "default", which will apply world/anyone rights on znodes
# and "sasl" which will give rights to the sasl/kerberos identity used to authenticate the nifi node
# The identity is determined using the value in nifi.kerberos.service.principal and the removeHostFromPrincipal
# and removeRealmFromPrincipal values (which should align with the kerberos.removeHostFromPrincipal and kerberos.removeRealmFromPrincipal
# values configured on the zookeeper server).
nifi.zookeeper.auth.type=
nifi.zookeeper.kerberos.removeHostFromPrincipal=
nifi.zookeeper.kerberos.removeRealmFromPrincipal=
# kerberos #
nifi.kerberos.krb5.file=
# kerberos service principal #
nifi.kerberos.service.principal=
nifi.kerberos.service.keytab.location=
# kerberos spnego principal #
nifi.kerberos.spnego.principal=
nifi.kerberos.spnego.keytab.location=
nifi.kerberos.spnego.authentication.expiration=12 hours
# external properties files for variable registry
# supports a comma delimited list of file locations
nifi.variable.registry.properties=
# analytics properties #
nifi.analytics.predict.enabled=false
nifi.analytics.predict.interval=3 mins
nifi.analytics.query.interval=5 mins
nifi.analytics.connection.model.implementation=org.apache.nifi.controller.status.analytics.models.OrdinaryLeastSquares
nifi.analytics.connection.model.score.name=rSquared
nifi.analytics.connection.model.score.threshold=.90
# runtime monitoring properties
nifi.monitor.long.running.task.schedule=
nifi.monitor.long.running.task.threshold=
# Create automatic diagnostics when stopping/restarting NiFi.
# Enable automatic diagnostic at shutdown.
nifi.diagnostics.on.shutdown.enabled=false
# Include verbose diagnostic information.
nifi.diagnostics.on.shutdown.verbose=false
# The location of the diagnostics folder.
nifi.diagnostics.on.shutdown.directory=./diagnostics
# The maximum number of files permitted in the directory. If the limit is exceeded, the oldest files are deleted.
nifi.diagnostics.on.shutdown.max.filecount=10
# The diagnostics folder's maximum permitted size in bytes. If the limit is exceeded, the oldest files are deleted.
nifi.diagnostics.on.shutdown.max.directory.size=10 MB
Users.xml:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<tenants>
<groups>
<group identifier="39903356-0181-1000-0000-000047f790c3" name="Admin">
<user identifier="3989a18a-0181-1000-0000-0000280a357e"/>
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
<user identifier="6d337594-bfba-3a95-88a7-01ec124f0bdb"/>
<user identifier="a98e60ec-bb80-35c6-bd31-1d1c7562a5a8"/>
<user identifier="2e8a3365-86df-3c2d-8614-7cf2c61cc5d1"/>
</group>
</groups>
<users>
<user identifier="2e8a3365-86df-3c2d-8614-7cf2c61cc5d1" identity="C=US, ST=xxx, O=xxx, OU=xxx, CN=xxxx"/>
<user identifier="a98e60ec-bb80-35c6-bd31-1d1c7562a5a8" identity="C=US, ST=xxx, O=xxx, OU=xxx, CN=xxx"/>
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e" identity="xxx@xxx.com"/>
<user identifier="6d337594-bfba-3a95-88a7-01ec124f0bdb" identity="C=US, ST=xxx, O=xxx, OU=xxxx, CN=xxxxx"/>
<user identifier="3989a18a-0181-1000-0000-0000280a357e" identity="abc@abc.com"/>
</users>
</tenants>
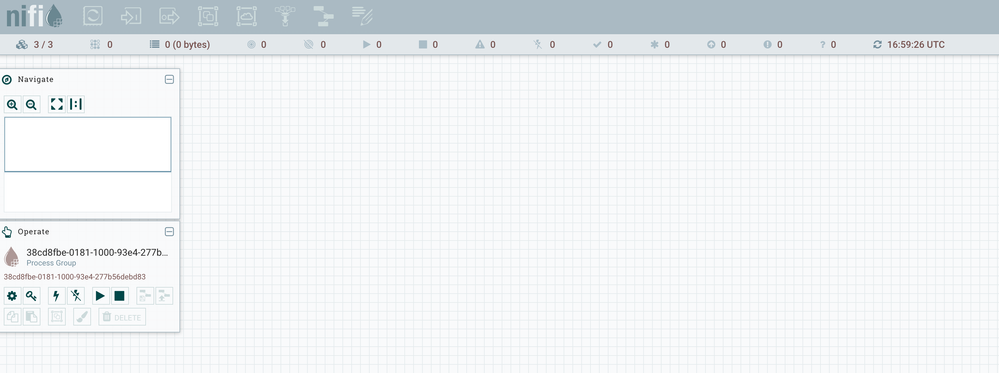
I am using SAML and successfully able to login as an Initial Admin Identity. However after login I can see my UI as seen in image, where all he processors are disabled for me.
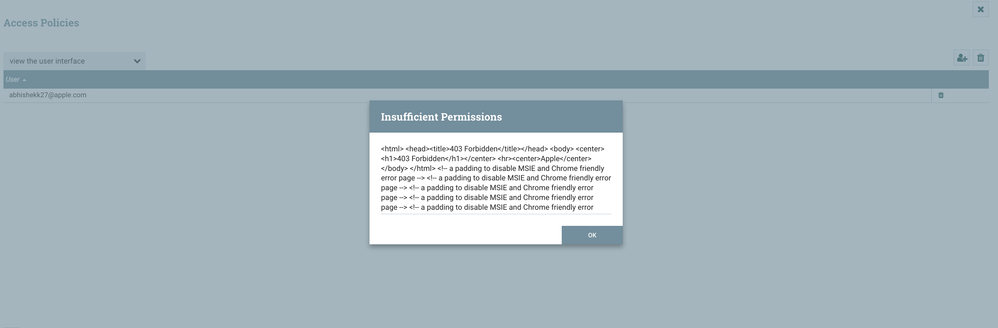
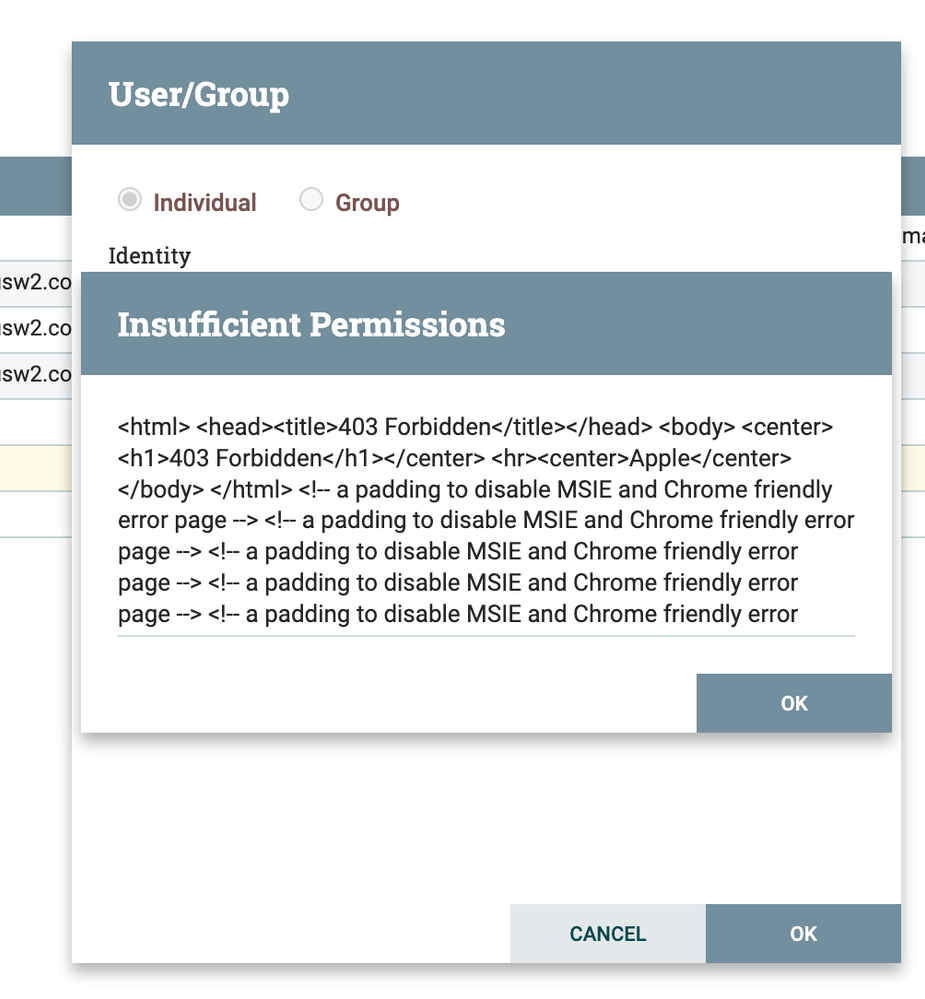
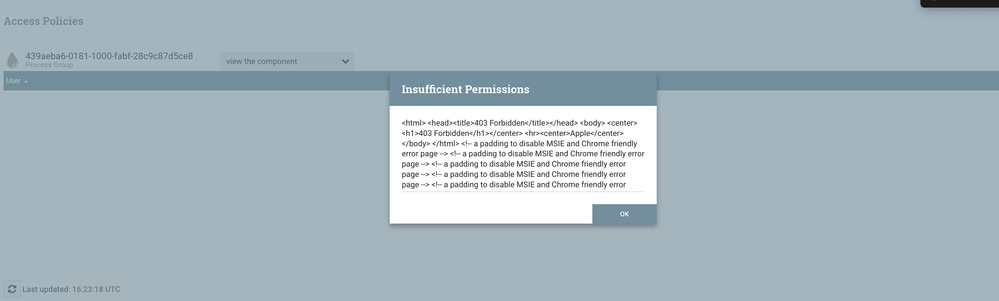
And if I perform any action like logout or add/edit user, add policy.... I get below error message:
I have similar setup with NIFI version 1.10.0, and it is working fine. But with Nifi-1.15.0 or Nifi-1.16.0 I am unable to perform any action.
Any help would be highly appreciated.
Created 06-21-2022 11:23 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you everyone for all the support and help.
RCA: What I have observed, whenever we are performing PUT or Delete HTTP requests, the proxy in front of NiFi is intercepting and denying the request. Hence these requests are not even reaching our EC2 instance, and NIFI request.log is not capturing any PUT/DELETE HTTP requests. Hence on UI, we are getting 403 permissions Issues.
Solution: We have enabled Put/ Delete HTTP requests from the proxy, and are now able to perform all the actions.
Hence we can close this ticket.
Created 06-07-2022 02:12 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
how do you log in to the site? do you use the same user that the certificate is created against which should be as specified in the "Initial admin property" in the authorizers.xml file?
Created 06-07-2022 10:46 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Certificates are for cluster Nodes. As I am using SAML, so I have set my email DI as Initial admin property. And while authenticating calls are redirected to my SAML service and they are authenticating my user.
Please let me know if I am missing something.
Created 06-08-2022 05:19 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you changed anything in the authorizers file after setting it up the first time. If so try deleting "users.xml" and "authorizations.xml" files and restart nifi. Those files will be re created based on the latest setup in the authorizers.xml
Created 06-08-2022 07:46 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have restarted NIFI by deleting "authorisations.xml " and "users.xml"
My authorisations.xml:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<authorizations>
<policies>
<policy identifier="f99bccd1-a30e-3e4a-98a2-dbc708edc67f" resource="/flow" action="R">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="91b40b98-fd71-37df-b47f-0b6bfc9495a3" resource="/data/process-groups/040813bd-98b2-35d7-9202-cc93f4873b91" action="R">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
<user identifier="2e8a3365-86df-3c2d-8614-7cf2c61cc5d1"/>
<user identifier="a98e60ec-bb80-35c6-bd31-1d1c7562a5a8"/>
<user identifier="6d337594-bfba-3a95-88a7-01ec124f0bdb"/>
</policy>
<policy identifier="b855b111-a013-30b7-828f-8c97c4dd5451" resource="/data/process-groups/040813bd-98b2-35d7-9202-cc93f4873b91" action="W">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
<user identifier="2e8a3365-86df-3c2d-8614-7cf2c61cc5d1"/>
<user identifier="a98e60ec-bb80-35c6-bd31-1d1c7562a5a8"/>
<user identifier="6d337594-bfba-3a95-88a7-01ec124f0bdb"/>
</policy>
<policy identifier="0e420cf9-3421-30ec-aab3-897e5bf63106" resource="/process-groups/040813bd-98b2-35d7-9202-cc93f4873b91" action="R">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="3e78b62e-721b-336f-a898-70534c5aa1a9" resource="/process-groups/040813bd-98b2-35d7-9202-cc93f4873b91" action="W">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="b8775bd4-704a-34c6-987b-84f2daf7a515" resource="/restricted-components" action="W">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="627410be-1717-35b4-a06f-e9362b89e0b7" resource="/tenants" action="R">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="15e4e0bd-cb28-34fd-8587-f8d15162cba5" resource="/tenants" action="W">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="ff96062a-fa99-36dc-9942-0f6442ae7212" resource="/policies" action="R">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="ad99ea98-3af6-3561-ae27-5bf09e1d969d" resource="/policies" action="W">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="2e1015cb-0fed-3005-8e0d-722311f21a03" resource="/controller" action="R">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="c6322e6c-4cc1-3bcc-91b3-2ed2111674cf" resource="/controller" action="W">
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
</policy>
<policy identifier="287edf48-da72-359b-8f61-da5d4c45a270" resource="/proxy" action="W">
<user identifier="2e8a3365-86df-3c2d-8614-7cf2c61cc5d1"/>
<user identifier="a98e60ec-bb80-35c6-bd31-1d1c7562a5a8"/>
<user identifier="6d337594-bfba-3a95-88a7-01ec124f0bdb"/>
</policy>
</policies>
</authorizations>
Here my user Identifier is:
<user identifier="5c72646f-a9cb-3239-9450-2511231b004e"/>
But still, I am unable to perform any actions as mentioned in my Post earlier.
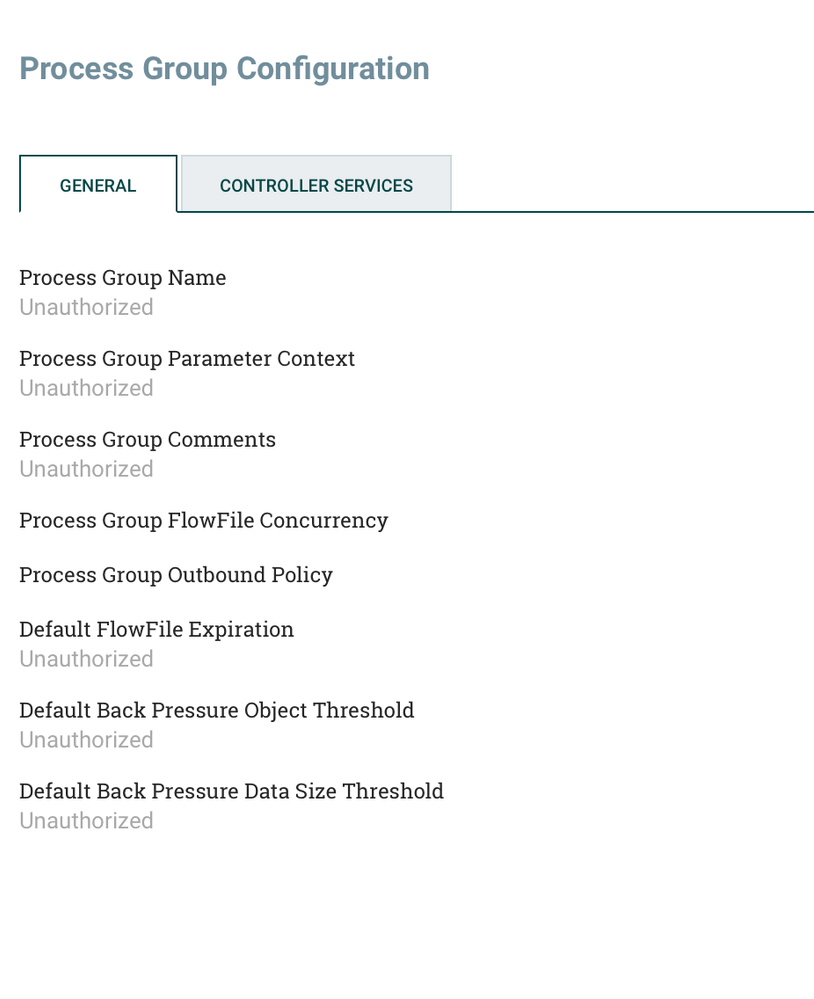
I have also observed, that it shows unauthorised for main process group:
Created 06-08-2022 08:18 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
These are the list of permissions I have to ADMIN User:
{
"identity": "xxxx@xxx.com",
"anonymous": false,
"provenancePermissions": {
"canRead": false,
"canWrite": false
},
"countersPermissions": {
"canRead": false,
"canWrite": false
},
"tenantsPermissions": {
"canRead": true,
"canWrite": true
},
"controllerPermissions": {
"canRead": true,
"canWrite": true
},
"policiesPermissions": {
"canRead": true,
"canWrite": true
},
"systemPermissions": {
"canRead": false,
"canWrite": false
},
"parameterContextPermissions": {
"canRead": true,
"canWrite": true
},
"restrictedComponentsPermissions": {
"canRead": false,
"canWrite": true
},
"componentRestrictionPermissions": [
{
"requiredPermission": {
"id": "read-distributed-filesystem",
"label": "read distributed filesystem"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "access-keytab",
"label": "access keytab"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "export-nifi-details",
"label": "export nifi details"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "read-filesystem",
"label": "read filesystem"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "access-environment-credentials",
"label": "access environment credentials"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "execute-code",
"label": "execute code"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "access-ticket-cache",
"label": "access ticket cache"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "write-filesystem",
"label": "write filesystem"
},
"permissions": {
"canRead": false,
"canWrite": true
}
},
{
"requiredPermission": {
"id": "write-distributed-filesystem",
"label": "write distributed filesystem"
},
"permissions": {
"canRead": false,
"canWrite": true
}
}
],
"canVersionFlows": false
}Created 06-10-2022 07:33 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Abhishek27Apple
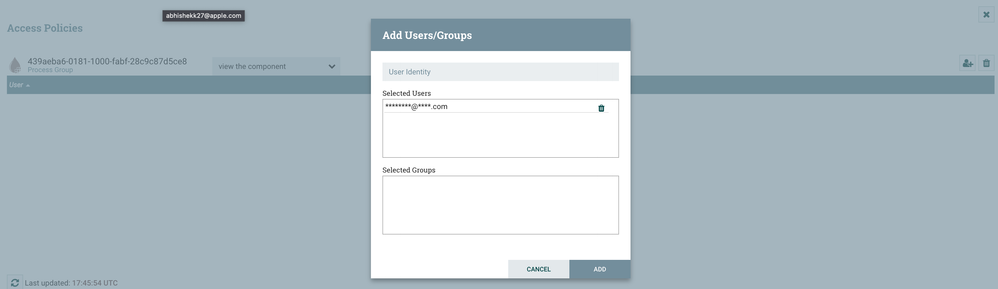
I don't see in your authorizations for your user where you have granted permissions for the root process group. From the UI you will see an "Operate" panel on the left side of the canvas. Within the "Operate" panel you will see the component currently selected and an icon that looks like a key. With Nothing selected, it defaults to the root process group created when NiFi was started the very first time.
Click on that key and add your user to the policies you want your user to have.
By default these policies are not set for the admin as they are not needed by an admin. These policies are typically used by developers who will be building dataflows on the canvas.
You can find all the access policies in the embedded documentation within NiFi or from the Apache NiFi site:
https://nifi.apache.org/docs/nifi-docs/html/administration-guide.html#access-policies
If you found this response assisted with your query, please take a moment to login and click on "Accept as Solution" below this post.
Thank you,
Matt
Created 06-10-2022 07:44 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Abhishek27Apple
Something that strikes me as odd in the configuration file authorizers.xml you shared, I don't see the
managed-authorizerThat provider would look like this and come after the file-user-group-provider and the file-access-policy-provider:
<authorizer>
<identifier>managed-authorizer</identifier>
<class>org.apache.nifi.authorization.StandardManagedAuthorizer</class>
<property name="Access Policy Provider">file-access-policy-provider</property>
</authorizer>
The nifi.properties file you shared is configured to use this authorizer. However, I would have expected NiFi to fail to start if this authorizer was really missing.
Matt
Created 06-10-2022 10:33 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @MattWho,
Thank you for replying, it's my bad, I have missed posting my complete authorizers.xml which have
<authorizer>
<identifier>managed-authorizer</identifier>
<class>org.apache.nifi.authorization.StandardManagedAuthorizer</class>
<property name="Access Policy Provider">file-access-policy-provider</property>
</authorizer>Created on 06-10-2022 10:55 AM - edited 06-10-2022 10:56 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MattWho
I have tried to click on that key and add my user to the policies. But still, it gives me 403 insufficient permissions :
Please find the Request/Response Details:
Request URL: https://xxxxxxxxxxxxxxx/nifi-api/policies/43f0b681-0181-1000-ffff-ffffc15af0d7
Request Method: PUT
Status Code: 403
Payload: ion":{"clientId":"4eb9cca3-0181-1000-5ccc-79d4aacc5540","version":0},"disconnectedNodeAcknowledged":false,"component":{"id":"43f0b681-0181-1000-ffff-ffffc15af0d7","users":[{"revision":{"version":0},"id":"5c72646f-a9cb-3239-9450-2511231b004e","permissions":{"canRead":true,"canWrite":true},"component":{"id":"5c72646f-a9cb-3239-9450-2511231b004e","identity":"*****@*******.com","configurable":true}}],"userGroups":[]}}
Response:
<html>
<head><title>403 Forbidden</title></head>
<body>
<center><h1>403 Forbidden</h1></center>
<hr><center>Apple</center>
</body>
</html>
If I am trying to add any policy to my user, it is giving me insufficient permissions.
Thank you!!!