Support Questions
- Cloudera Community
- Support
- Support Questions
- NiFi LDAP authorization issue
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
NiFi LDAP authorization issue
- Labels:
-
Apache NiFi
Created 04-10-2023 05:39 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Team,
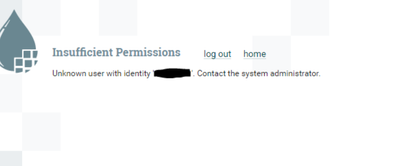
I have configured the ldap connection for nifi login, when I try to access the nifi in web UI I am getting error like "Insufficient Permission Unknow user with identity 'xyz123' Contact the system administrator". Authentication is happing successfully, but authorization is not happening could you please advice.
Created 04-10-2023 11:40 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@apmmahesh
Authentication and Authorization are two separate process in NiFi. Successful Authentication will result in an user identity string (case sensitive) which is then passed to the authorization process to verify if the that identity string has been authorized for the requested resource. In order to access the NiFI UI, users must be authorized to "view the user interface".
The authorization is configured in the authorizers.xml. I am not sure which authorizer or providers you are using. Most commonly used is the managed authorizer, File-access-policy-provider, and File-user-group-provider. But you might also be using the ldap-user-group-provider.
The file-access-policy-provider is used to setup necessary policies for the initial admin and nodes (if multi-node NiFi cluster) in an authorizations.xml file. Within the file-access-policy provider you would define your initial admin user identity string "xyz123" so that the polcies need to be admin are assigned to this user identity. Keep in mind the file-access-policy provider will only generate an authorizations.xml file if it does NOT already exist. So if you edit the initial admin or NiFi nodes later, this changes willl not be reflected in the already existing authorizations.xml. You'll need to delete current so new is generated.
Before the file access-policy-provider can setup initial admin policies for user "xyz123", the authorizer needs to be able to return that user identity (case sensitive) from one of the configured user-group-provider configured on the authorizers.xml. You can use the file-user-group-provider to manually add user identities to NiFi for purpose of setting up aithorization (in this case their is an initial user identity 1 property you would add "xyz123" to. Optionally you can setup the ldap-user-group-provider to sync user and group identities from your ldap server. Keep in mind that two providers can not return the same identity. So if you are syncing from LDAP, don't configure the same user identity in the file-user-group-provider.
here are the relevant Apache NiFi docs on these providers:
https://nifi.apache.org/docs/nifi-docs/html/administration-guide.html#fileusergroupprovider
https://nifi.apache.org/docs/nifi-docs/html/administration-guide.html#ldapusergroupprovider
https://nifi.apache.org/docs/nifi-docs/html/administration-guide.html#composite-implementations
https://nifi.apache.org/docs/nifi-docs/html/administration-guide.html#fileaccesspolicyprovider
https://nifi.apache.org/docs/nifi-docs/html/administration-guide.html#standardmanagedauthorizer
If you found that the provided solution(s) assisted you with your query, please take a moment to login and click Accept as Solution below each response that helped.
Thank you,
Matt
Created on 04-11-2023 02:44 AM - edited 04-11-2023 02:52 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@MattWho Thanks for the clarification, please find the below authorizers.xml and login-identity-providers.xml files. correct me if I am wrong mean.
authorizers.xml
<accessPolicyProvider>
<identifier>file-access-policy-provider</identifier>
<class>org.apache.nifi.authorization.FileAccessPolicyProvider</class>
<property name="User Group Provider">file-user-group-provider</property>
<property name="Authorizations File">./conf/authorizations.xml</property>
<property name="Initial Admin Identity 1">CN=admin, OU=NIFI</property>
<property name="Initial Admin Identity 2">xyz123</property>
<property name="Legacy Authorized Users File"></property>
<property name="Node Identity 1">CN=nifi1.li.xyz.net, OU=NIFI</property>
<property name="Node Identity 2">CN=nifi2.li.xyz.net, OU=NIFI</property>
<property name="Node Identity 3">CN=nifi3.li.xyz.net, OU=NIFI</property>
<property name="Node Group"></property>
</accessPolicyProvider>
<userGroupProvider>
<identifier>file-user-group-provider</identifier>
<class>org.apache.nifi.authorization.FileUserGroupProvider</class>
<property name="Users File">./conf/users.xml</property>
<property name="Legacy Authorized Users File"></property>
<property name="Initial User Identity 1">CN=admin, OU=NIFI</property>
<property name="Initial User Identity 2">CN=nifi1.li.xyz.net, OU=NIFI</property>
<property name="Initial User Identity 3">CN=nifi2.li.xyz.net, OU=NIFI</property>
<property name="Initial User Identity 4">CN=nifi3.li.xyz.net, OU=NIFI</property>
</userGroupProvider>
<authorizer>
<identifier>managed-authorizer</identifier>
<class>org.apache.nifi.authorization.StandardManagedAuthorizer</class>
<property name="Access Policy Provider">file-access-policy-provider</property>
</authorizer>
login-identity-providers.xml
<provider>
<identifier>ldap-provider</identifier>
<class>org.apache.nifi.ldap.LdapProvider</class>
<property name="Authentication Strategy">SIMPLE</property>
<property name="Manager DN">ldap@li.xyz.net</property>
<property name="Manager Password">Password</property>
<property name="TLS - Keystore"></property>
<property name="TLS - Keystore Password"></property>
<property name="TLS - Keystore Type"></property>
<property name="TLS - Truststore"></property>
<property name="TLS - Truststore Password"></property>
<property name="TLS - Truststore Type"></property>
<property name="TLS - Client Auth"></property>
<property name="TLS - Protocol"></property>
<property name="TLS - Shutdown Gracefully"></property>
<property name="Referral Strategy">FOLLOW</property>
<property name="Connect Timeout">10 secs</property>
<property name="Read Timeout">10 secs</property>
<property name="Url">ldap://ldap.li.xyz.net/</property>
<property name="User Search Base">DC=li,DC=xyz,DC=net</property>
<property name="User Search Filter">sAMAccountName={0}</property>
<property name="Identity Strategy">USE_USERNAME</property>
<property name="Authentication Expiration">12 hours</property>
</provider>
nifi.properties
nifi.login.identity.provider.configuration.file=./conf/login-identity-providers.xml
nifi.security.user.login.identity.provider=ldap-provider
Note: user CN=admin OU=NIFI I am able to login with certification, but ldap user xyz123 is facing "Insufficient Permission Unknow user with identity 'xyz123' Contact the system administrator" issue.
Created 04-12-2023 08:58 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@apmmahesh
I see one issue with your shared authorizers.xml configuration.
The file loads the various providers from the top down, so it is VERY important that if a provider has a dependency on another provider that the provider it is dependent on is loaded first.
So in your authorizers.xml has the following loading order:
file-access-policy-provider --> file-user-grouo-provider --> managed-authorizerThe problem here is that the file-access-policy provider is dependent on the file-user-group-provider which has not been loaded yet. so it will not set default policies correctly when generating the authorizations.xml file.
Move the file-access-policy-provider between fie-user-group-provider (top of authorizers.xml) and managed-authorizer (bottom of authorizers.xml).
Second issue is that you have properties "Initial Admin Identity 1" and "Initial Admin Identity 2" properties in your file-access-policy-provider. These are not real properties. You can only specify one "Initial Admin Identity" in the file-access-policy-provider. These unexpected property names would just be ignored.
Third issue is that you need to not only specify your "Initial Admin Identity" in the file-access-policy-provider, but also need to make sure that the same user identity string is being defined in the "file-user-group-provider as another "initial User Identity <num>". NiFi can't seed policies for a user Identity it does know about.
Also keep in mind that changes to authorizers.xml file-access-policy-provider and file-access-policy-provider configuration will not result in modification of existing users.xml and authorizations.xml files. You'll need to remove these so that new are created on startup of NiFi.
Now if you can already login with your "CN=Admin, OU=NiFi" certificate and at time of that setup the users.xml and authorizations.xml was created correctly, you can use this admin user to access "users" from global menu in NiFi and add your additional user "xyz123" and then set policies you want user xyz123 to have.
If you found that the provided solution(s) assisted you with your query, please take a moment to login and click Accept as Solution below each response that helped.
Thank you,
Matt