Support Questions
- Cloudera Community
- Support
- Support Questions
- Re: Nifi cluster authorization error
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Nifi cluster authorization error
- Labels:
-
Apache NiFi
Created on 09-18-2022 07:48 PM - edited 09-18-2022 07:51 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I used nifi 1.13.2 cluster of 2 nodes.
Node1 is rhel7, node2 is redos, embedded Zookeeper.
The cluster works correctly (nodes see each other, the coordinator is selected.)
Certificates on nodes are self-signed.
Faced with the problem of authorization in the UI.
LDAP authorization does not work (without cluster the LDAP authorization worked on both nodes).
I am trying to connect to node1.
When I enter my username and password, I return back to the authorization page.
The log on the node1:
2022-09-19 05:36:14,892 INFO [NiFi Web Server-258] o.a.n.w.s.NiFiAuthenticationFilter Attempting request for (<JWT token>) GET https://node1.domain.ru:8080/nifi-api/flow/current-user (source ip: <IP node1>)
2022-09-19 05:36:14,895 INFO [NiFi Web Server-258] o.a.n.w.s.NiFiAuthenticationFilter Authentication success for <user name>
2022-09-19 05:36:14,895 DEBUG [NiFi Web Server-258] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:14,895 DEBUG [NiFi Web Server-258] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:14,895 DEBUG [NiFi Web Server-258] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:14,901 DEBUG [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: null
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-276] o.a.n.w.s.x509.X509AuthenticationFilter Raw X-ProxiedEntitiesChain - <<user name>>
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-276] o.a.n.w.s.x509.X509AuthenticationFilter Raw X-ProxiedEntityGroups - <>
2022-09-19 05:36:14,902 INFO [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Attempting request for (<<user name>><CN=node1.domain.ru, OU=NIFI>) GET https://node1.domain.ru:8080/nifi-api/flow/current-user (source ip: <IP node1>)
2022-09-19 05:36:14,902 INFO [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Authentication success for <user name>
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-276] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: <user name>
2022-09-19 05:36:15,228 DEBUG [NiFi Web Server-248] o.a.n.w.s.x509.X509CertificateExtractor No client certificate found in request.
The log on the node2:
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: null
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-198] o.a.n.w.s.x509.X509CertificateExtractor No client certificate found in request.
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: null
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: null
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: null
2022-09-19 05:36:14,902 DEBUG [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Checking secure context token: null
2022-09-19 05:36:14,902 INFO [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Attempting request for (<anonymous>) GET https://node2.domain.ru:8080/nifi-api/flow/current-user (source ip: <IP node1>)
2022-09-19 05:36:14,903 WARN [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter Rejecting access to web api: Anonymous authentication has not been configured.
2022-09-19 05:36:14,903 DEBUG [NiFi Web Server-198] o.a.n.w.s.NiFiAuthenticationFilter
org.apache.nifi.web.security.InvalidAuthenticationException: Anonymous authentication has not been configured.
at org.apache.nifi.web.security.anonymous.NiFiAnonymousAuthenticationProvider.authenticate(NiFiAnonymousAuthenticationProvider.java:46)
at org.springframework.security.authentication.ProviderManager.authenticate(ProviderManager.java:174)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.authenticate(NiFiAuthenticationFilter.java:79)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.doFilter(NiFiAuthenticationFilter.java:59)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:331)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.authenticate(NiFiAuthenticationFilter.java:100)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.doFilter(NiFiAuthenticationFilter.java:59)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:331)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.authenticate(NiFiAuthenticationFilter.java:100)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.doFilter(NiFiAuthenticationFilter.java:59)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:331)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.authenticate(NiFiAuthenticationFilter.java:100)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.doFilter(NiFiAuthenticationFilter.java:59)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:331)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.authenticate(NiFiAuthenticationFilter.java:100)
at org.apache.nifi.web.security.NiFiAuthenticationFilter.doFilter(NiFiAuthenticationFilter.java:59)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:331)
at org.springframework.web.filter.CorsFilter.doFilterInternal(CorsFilter.java:96)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:331)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:214)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:177)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:347)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:263)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.filter.TimerFilter.doFilter(TimerFilter.java:51)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.filter.ExceptionFilter.doFilter(ExceptionFilter.java:46)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:201)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.eclipse.jetty.servlets.DoSFilter.doFilterChain(DoSFilter.java:487)
at org.eclipse.jetty.servlets.DoSFilter.doFilter(DoSFilter.java:336)
at org.eclipse.jetty.servlets.DoSFilter.doFilter(DoSFilter.java:301)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.security.headers.StrictTransportSecurityFilter.doFilter(StrictTransportSecurityFilter.java:48)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.security.headers.XContentTypeOptionsFilter.doFilter(XContentTypeOptionsFilter.java:48)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.security.headers.XSSProtectionFilter.doFilter(XSSProtectionFilter.java:48)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.security.headers.ContentSecurityPolicyFilter.doFilter(ContentSecurityPolicyFilter.java:47)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.apache.nifi.web.security.headers.XFrameOptionsFilter.doFilter(XFrameOptionsFilter.java:48)
at org.eclipse.jetty.servlet.FilterHolder.doFilter(FilterHolder.java:193)
at org.eclipse.jetty.servlet.ServletHandler$Chain.doFilter(ServletHandler.java:1601)
at org.eclipse.jetty.servlet.ServletHandler.doHandle(ServletHandler.java:548)
at org.eclipse.jetty.server.handler.ScopedHandler.handle(ScopedHandler.java:143)
at org.eclipse.jetty.security.SecurityHandler.handle(SecurityHandler.java:602)
at org.eclipse.jetty.server.handler.HandlerWrapper.handle(HandlerWrapper.java:127)
at org.eclipse.jetty.server.handler.ScopedHandler.nextHandle(ScopedHandler.java:235)
at org.eclipse.jetty.server.session.SessionHandler.doHandle(SessionHandler.java:1624)
at org.eclipse.jetty.server.handler.ScopedHandler.nextHandle(ScopedHandler.java:233)
at org.eclipse.jetty.server.handler.ContextHandler.doHandle(ContextHandler.java:1435)
at org.eclipse.jetty.server.handler.ScopedHandler.nextScope(ScopedHandler.java:188)
at org.eclipse.jetty.servlet.ServletHandler.doScope(ServletHandler.java:501)
at org.eclipse.jetty.server.session.SessionHandler.doScope(SessionHandler.java:1594)
at org.eclipse.jetty.server.handler.ScopedHandler.nextScope(ScopedHandler.java:186)
at org.eclipse.jetty.server.handler.ContextHandler.doScope(ContextHandler.java:1350)
at org.eclipse.jetty.server.handler.ScopedHandler.handle(ScopedHandler.java:141)
at org.eclipse.jetty.server.handler.HandlerCollection.handle(HandlerCollection.java:146)
at org.eclipse.jetty.server.handler.gzip.GzipHandler.handle(GzipHandler.java:763)
at org.eclipse.jetty.server.handler.ContextHandlerCollection.handle(ContextHandlerCollection.java:191)
at org.eclipse.jetty.server.handler.HandlerList.handle(HandlerList.java:59)
at org.eclipse.jetty.server.handler.HandlerWrapper.handle(HandlerWrapper.java:127)
at org.eclipse.jetty.server.Server.handle(Server.java:516)
at org.eclipse.jetty.server.HttpChannel.lambda$handle$1(HttpChannel.java:388)
at org.eclipse.jetty.server.HttpChannel.dispatch(HttpChannel.java:633)
at org.eclipse.jetty.server.HttpChannel.handle(HttpChannel.java:380)
at org.eclipse.jetty.server.HttpConnection.onFillable(HttpConnection.java:279)
at org.eclipse.jetty.io.AbstractConnection$ReadCallback.succeeded(AbstractConnection.java:311)
at org.eclipse.jetty.io.FillInterest.fillable(FillInterest.java:105)
at org.eclipse.jetty.io.ssl.SslConnection$DecryptedEndPoint.onFillable(SslConnection.java:540)
at org.eclipse.jetty.io.ssl.SslConnection.onFillable(SslConnection.java:395)
at org.eclipse.jetty.io.ssl.SslConnection$2.succeeded(SslConnection.java:161)
at org.eclipse.jetty.io.FillInterest.fillable(FillInterest.java:105)
at org.eclipse.jetty.io.ChannelEndPoint$1.run(ChannelEndPoint.java:104)
at org.eclipse.jetty.util.thread.strategy.EatWhatYouKill.runTask(EatWhatYouKill.java:336)
at org.eclipse.jetty.util.thread.strategy.EatWhatYouKill.doProduce(EatWhatYouKill.java:313)
at org.eclipse.jetty.util.thread.strategy.EatWhatYouKill.tryProduce(EatWhatYouKill.java:171)
at org.eclipse.jetty.util.thread.strategy.EatWhatYouKill.run(EatWhatYouKill.java:129)
at org.eclipse.jetty.util.thread.ReservedThreadExecutor$ReservedThread.run(ReservedThreadExecutor.java:383)
at org.eclipse.jetty.util.thread.QueuedThreadPool.runJob(QueuedThreadPool.java:882)
at org.eclipse.jetty.util.thread.QueuedThreadPool$Runner.run(QueuedThreadPool.java:1036)
at java.base/java.lang.Thread.run(Thread.java:834)
I will be glad of any help.
Created 09-29-2022 08:48 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello everyone, the problem was solved by replacing java Oracle openjdk-11.0.1.13 with java Liberica jdk11.0.16
Created 09-22-2022 07:41 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
JAVA
node1
o.a.zookeeper.server.ZooKeeperServer Server environment:java.version=11.0.11
o.a.zookeeper.server.ZooKeeperServer Server environment:java.vendor=Red Hat, Inc.
node2
o.a.zookeeper.server.ZooKeeperServer Server environment:java.version=11.0.1
o.a.zookeeper.server.ZooKeeperServer Server environment:java.vendor=Oracle Corporation
Created 09-23-2022 12:02 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
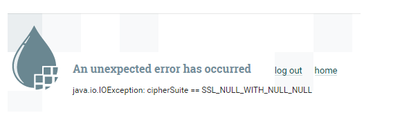
Today there was such an error, I didn't change anything in the configuration.
Created 09-23-2022 12:23 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
These errors are repeated periodically.
Created 09-29-2022 08:48 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello everyone, the problem was solved by replacing java Oracle openjdk-11.0.1.13 with java Liberica jdk11.0.16
- « Previous
-
- 1
- 2
- Next »