Support Questions
- Cloudera Community
- Support
- Support Questions
- Using ssl cert file for autentification in nif...
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Using ssl cert file for autentification in nifi
- Labels:
-
Apache NiFi
Created 08-29-2017 01:25 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I want to make workflow in nifi (via code and processors) that make the same job which is completed by rest api . I want to use certificate which i have exported from browser ( nifi uses ssl autentipication) now i want to know how can i import pem file into nifi and use it for autentipication?
Created on 08-29-2017 05:46 PM - edited 08-17-2019 05:08 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
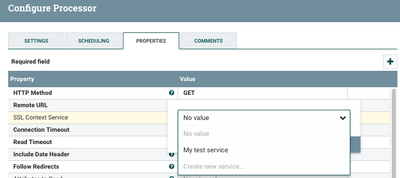
Many processors in NiFi support using a the NiFi "SSL Context Service". Looking at InvokeHTTP processor as an example:
You can create as many SSL context service as you want. Each can be configured to use its own keystore and truststore files.
There are plenty of resources on-line for taking your pem file and loading it into a PKCS12 (.p12 or .pfx file) keystore. For the truststore, I would suggest using the JKS truststore already in use by your secured NiFi.
Thanks,
Matt
Created 08-30-2017 08:58 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have exported my cer file into cacerts.jks and added it inside truststore in SSL context service ut it still shows me that service is invalid :truststore file validated agains cacerts.jks it is invalid because fail doesn;t exist or can;t be read but i can read cacerts.jks by keystore -list command what should i change to make service enable?
Created 08-30-2017 12:55 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What user own the running NiFi process? You need to make sure that user can read those keystore files. I suggest becoming that user on the NiFi server and making sure you can change directories to the location of cacerts.jks file. Also as that user run the keytool list command.
keytool -v --list -keystore <path to keystore>/cacerts.jks
The keystore file must contain a "PrivateKeyEntry" for your user. (The issuer will be the user if it is self-signed or it will be a CA if it was signed by a CA.)
The truststore file must contain a "trustedCertEntry" for your user (self-signed) or the CA that signed the cert for you user.
Also make sure that these files exist in the same location on every node if you are running a NiFi cluster.
Thanks,
Matt
Created 08-31-2017 05:49 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In case i am logged in properly in nifi will i neeed ssl handshake when i use rest api commands like this /flowfile-queues/{id}/drop-requests , i think i haven't configured autentification right that's why i can't use rest api inside invokehttp processor
Created 08-31-2017 12:39 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The user who is logged in and building out dataflow, has no correlation to who that dataflow is running as. All the processors on the canvas are being executed by the user who owns the Nifi process itself. So when you setup a SSL Context Service to use a specific keystore and truststore, it is the PrivateKeyEntry in that keystore that will be used as the user for authentication and authorization during any established connection. The TrustedCertEntry(s) in the truststore provided in the SSL Context Service will be used to establish trust of the Server certificates passed by the endpoint (in your case the certs being passed from your NiFi nodes) during the two-way TLS handshake.
Now this is a little different then when you log in via the browser to the UI. Two-way TLS is not enforced by your browser like it is by NiFi's processors. Your browser likely did not trust the cert presented by your NiFI nodes, and you added an exception the first time you connected saying that you would like to trust that unknown cert coming from the nifi node. Within NiFi and the SSL Context Service, there is no way to add such an exception. So trust must work in both directions. This means the truststore you use in your ssl Context Service must be able to trust the certificates being passed by each of your Nifi nodes.
Thanks,
Matt