Community Articles
- Cloudera Community
- Support
- Community Articles
- Configure Knox SSO and Knox Proxy for NiFi UI Acce...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Created on
02-14-2020
04:18 PM
- edited on
02-14-2020
05:15 PM
by
ask_bill_brooks
This document seeks to explain the configuration steps required to access NiFi UI using Knox SSO and along with Knox proxy.
This eliminates the need to access NiFi UI using the regular port 9091 on the NiFi node
Configure Knox SSO for NiFi:
Create the CA signed Knox certificate:
Ensure that Knox certificate is signed with the same CA that NiFi certificates are signed. By default, knox creates a self-signed certificate which needs to be replaced by CA signed cert.
Go to knox server and do the following:
Copy the CA signed certificate from the knox host as gateway.jks in the knox keystore path.
$ cp /etc/security/certs/keystore.jks /var/lib/knox/data-3.1.0.0-78/security/keystores/gateway.jks
$ chown knox:knox /var/lib/knox/data-3.1.0.0-78/security/keystores/gateway.jks
Knox certificate’s keystore password should match the knox master secret (let us say, it is Hadoop*123)
Now, let us change the new knox certificate’s password:
$ keytool -storepasswd -keystore /var/lib/knox/data-3.1.0.0-78/security/keystores/gateway.jks
Enter existing password: <changeit>
New password: <Hadoop*123>
Re-enter new password:
Change key's password for knox certificate:
$ keytool -keypasswd -alias gateway-identity -keystore /var/lib/knox/data-3.1.0.0-78/security/keystores/gateway.jks
enter keystore password: <Hadoop*123>
enter key's existing password: <changeit>
enter key's new password: <Hadoop*123>
Restart Knox service using ambari UI
Deploy Knox Certificate on NiFi Nodes:
Run the following commands on all NiFi nodes:
Ensure that the correct knox server is used in the below command.
$ openssl s_client -connect knox.example.com:8443</dev/null| openssl x509 -out /usr/hdf/current/nifi/conf/knox.pem
$ chown nifi:nifi /usr/hdf/current/nifi/conf/knox.pem
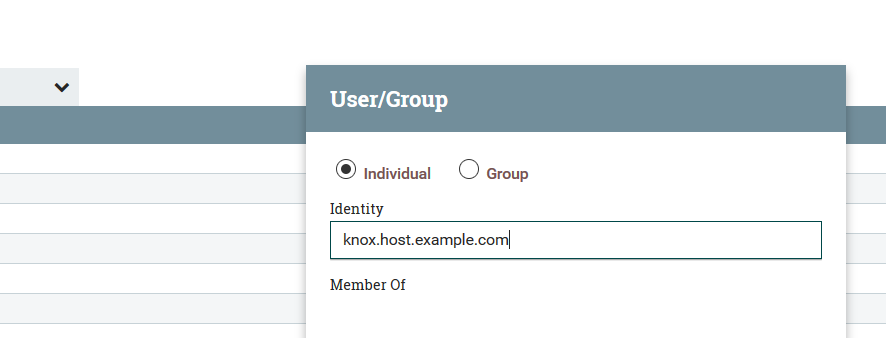
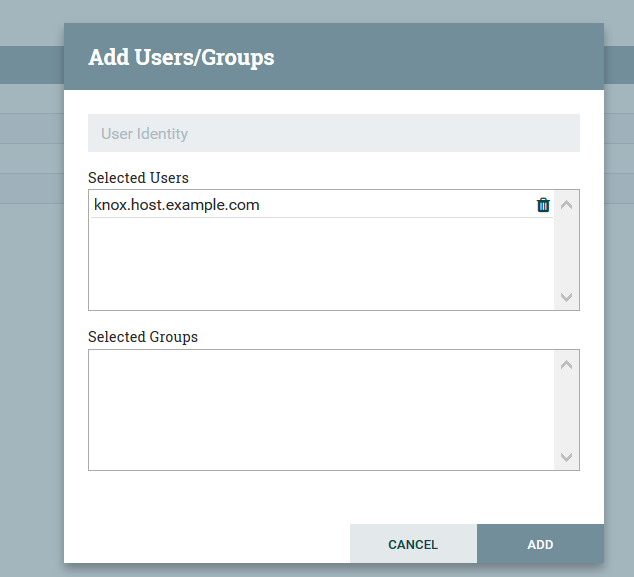
Add Knox hostname as a user in NiFi UI:
This step is very important, and needs to be done before modifying nifi configurations and restarting nifi
Login to NiFi UI as the admin user and add Knox hostname as a user and add the proxy request privilege to the Knox host user.
Once knox DN is added as user, go to policies, select the policy “proxy user requests” and click on add user button. Select the knox host user you just added and click on ADD.
NiFi Configuration changes in Ambari UI:
Login to HDF Ambari UI make the following configuration changes.
Get the Knox server DN from knox certificate. For this:
Login to knox server and run the command:
$ keytool -list -keystore /var/lib/knox/data-3.1.0.0-78/security/keystores/gateway.jks -v
Enter the keystore password: <Hadoop*123>
Look for the word “gateway-identity” in the output and capture the DN of the “owner”. It will look something like this CN=knox.host.example.com,
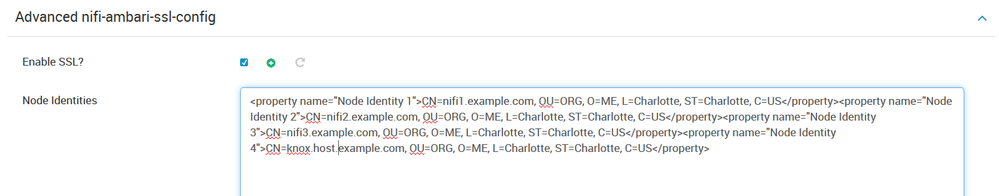
Add the DN obtained from above step, and add it as a node identity in NiFi configuration as shown below. The last entry in the screen shot is the knox DN:
Advanced nifi-ambari-ssl-config:
nifi.security.needClientAuth = true
Add an entry in the “node identities” check box on ambari nifi configuration page, and add the full DN of the knox host from the knox certificate.
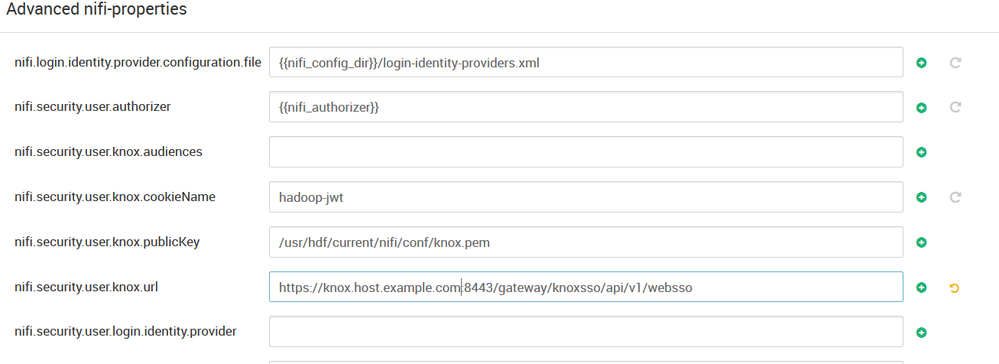
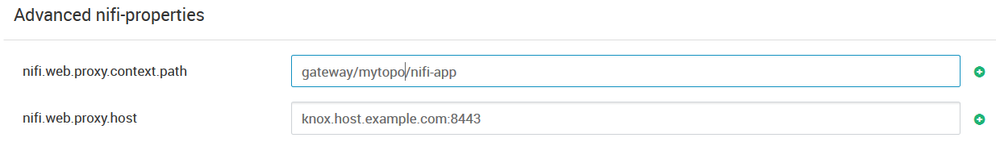
Advanced nifi-properties:
Make the following changes in ambari.
Please note that nifi.security.user.login.identity.provider should be empty when you configure for knox SSO. Usually we see “ldap-provider” in this property. If you see it, make it empty.
In the following configuration, replace “mytopo” with the name of the “topology” name. the knox host name and port should be entered in “nifi.web.proxy.host”
Restart NiFi service on ambari
Knox proxy configuration:
Configure Knox proxy in your knox topology file by adding below entries in the file. The topology file should be owned by “knox” user.
<topology>
<gateway>
<provider>
<role>federation</role>
<name>SSOCookieProvider</name>
<enabled>true</enabled>
<param>
<name>sso.authentication.provider.url</name>
<value>https://knox.host.example.com:8443/gateway/knoxsso/api/v1/websso</value>
</param>
</provider>
<provider>
<role>identity-assertion</role>
<name>Default</name>
<enabled>true</enabled>
</provider>
</gateway>
<service>
<role>NIFI</role>
<url>https://nifi1.example.com:9091</url>
<url>https://nifi2.example.com:9091</url>
<url>https://nifi3.example.com:9091</url>
<param>
<name>useTwoWaySsl</name>
<value>true</value>
</param>
</service>
</topology>
Add the NiFi IP addresses and host name into your windows hosts file (if you are using private IPs)
Once it is done, enter the following url in the browser:
https://knox.host.example.com:8443/gateway/mytopo/nifi-app/nifi
It will take you to the knox SSO page, and then you can enter the user credentials and it will take you to the NiFi UI canvas.