Community Articles
- Cloudera Community
- Support
- Community Articles
- Securing NiFi Step-by-Step
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Created on 10-05-2015 02:43 PM - edited 08-17-2019 02:22 PM
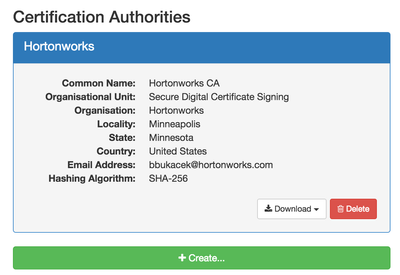
Note: I used TinyCert to generate my own certificate authority and certificates. Probably the easiest way to generate new certificates Create your own certificate authority. Fill in your own values.
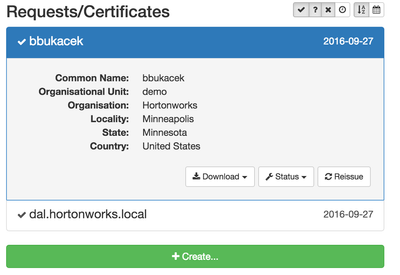
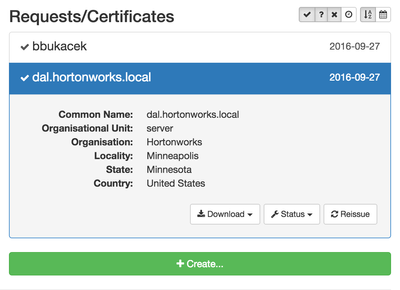
Create 2 new certificates. One is your client certificate (in this case, bbukacek) and a server certificate which will be used for the NiFi keystore.
Client Certificate
Server Certificate
Download the certificate authority, the client and server certificates and upload to your NiFi environment.
Note: Easiest way is to download the client and server certificates in PKCS12 format Create a TrustStore We will use the certificate authority to create the TrustStore. Use the following syntax to create the TrustStore:
> keytool -import -file <ca_file>.pem -alias cacert -keystore truststore.jks -storepass <password> Configure NiFi Now that the TrustStore is created we can configure NiFi Keystore and TrustStore.
Under $NIFI_HOME/conf, open the nifi.properties.
Set the web properties First and this important, unset the property nifi.web.http.port since once the configuration is completed will be communicating with NiFi over SSL.
Set the following web properties:
nifi.web.https.host=<nifi_hostname>
nifi.web.https.port=<port> :: Typically 8443, but pick a port
Configure the Keystore To configure the keystore we will be using the server certificate that was downloaded. Put the certificate in a location that can be referenced for the property. For the keystore there are 3 properties to set.
nifi.security.keystore=<path_to_keystore_file>
nifi.security.keystoreType=PKCS12
nifi.secuirty.keystorePasswd=<keystore_password>
Configure the TrustStore To configure the TrustStore we will use the TrustStore that we created above. Again, put the certificate in a location that can be reference for the property. For the truststore there are 3 properties to set.
nifi.security.truststore=<path_to_truststore_file>
nifi.security.truststoreType=JKS
nifi.security.truststorePasswd=<truststore_password>
Lastly, property to set for client authentication. For explanation, see the following Apache NiFi docs: https://nifi.apache.org/docs.html
nifi.security.needClientAuth=true
Configure NiFi Admin User
Open the file authorized-users.xml, in the $NIFI_HOME/conf directory and create an admin user based off the DN from the client certificate.
<users>
<user dn="CN=bbukacek, OU=demo, O=Hortonworks, L=Minneapolis, ST=Minnesota, C=US">
<role name="ROLE_ADMIN"/>
</user>
</users>
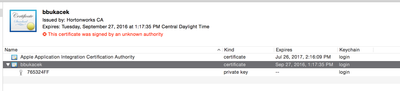
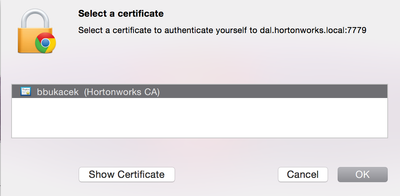
Add Certificate to Browser If you downloaded the client certificate, double-click on it and will be added to the KeyChain Access (Mac).
Log into NiFi https://<host>:8443/nifi
The browser should ask for a certificate to select.
As the Admin user, access for other users can be controlled from the NiFi UI.
Created on 11-16-2015 01:11 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great write-up, Brad! I appreciate you taking the time to write this up with screenshots and all!
Created on 10-30-2016 08:25 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Brad,
Is this guide still valid? I can't get it to work.
Best
Bojan
Created on 10-31-2016 06:08 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Bojan, if you are using Apache NiFi 1.0.0 or later, use this guide by @Bryan Bende.