Support Questions
- Cloudera Community
- Support
- Support Questions
- CDP 7.1.6 Ranger KMS test conection failed " User...
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Float this Question for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
CDP 7.1.6 Ranger KMS test conection failed " User:ranger not allowed to do 'GET_KEYS' "
- Labels:
-
Apache Ranger
-
Cloudera on premises
Created on
06-25-2021
04:25 PM
- last edited on
04-21-2026
02:01 AM
by
GrazittiAPI
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Gurus,
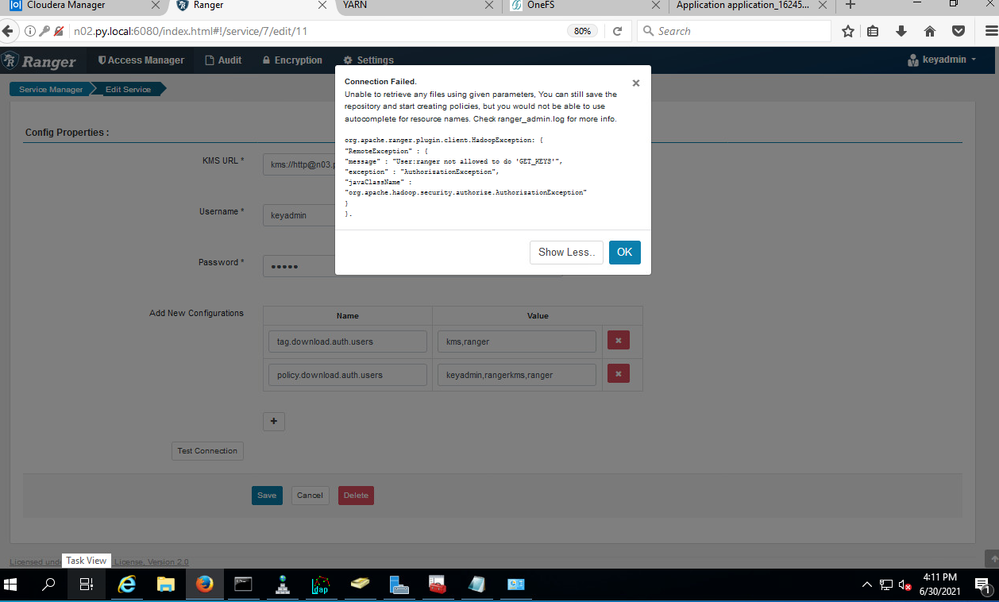
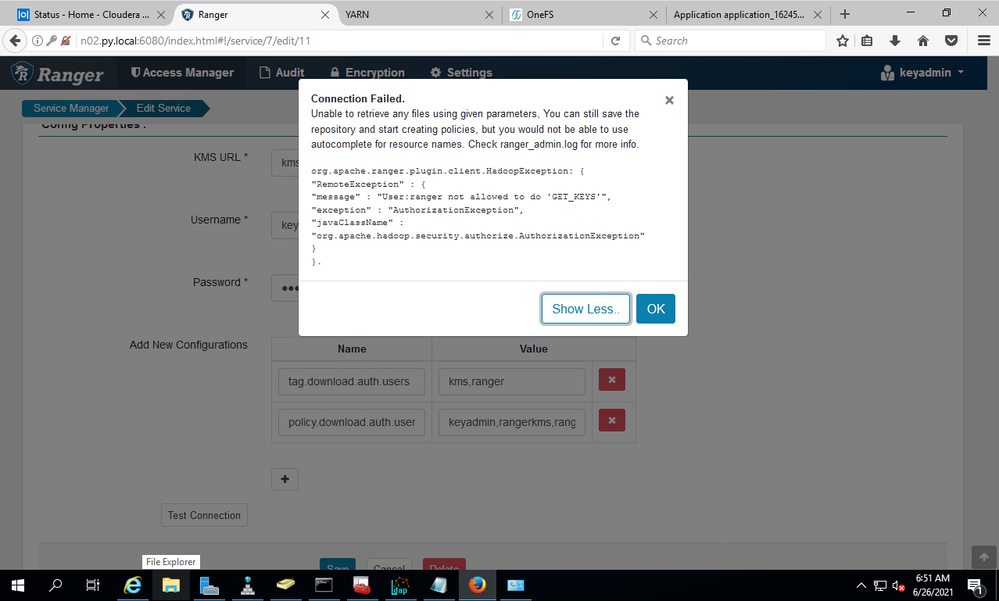
I am having Ranger KMS test connection failed, it is POC test.
CDP 7.1.6 with Isilon OneFS v8.2.2.0, AD kerberos enabled.

Already added following lines in kms-site.xml ( added in Ranger KMS -configuration )
hadoop.kms.proxyuser.rangeradmin.hosts=*
hadoop.kms.proxyuser.rangeradmin.groups=*
hadoop.kms.proxyuser.rangeradmin.users=*
Ranger KMS debug:
2021-06-26 06:51:38,420 DEBUG org.apache.ranger.plugin.classloader.RangerPluginClassLoader: ==> RangerPluginClassLoader.deactivate()
2021-06-26 06:51:38,420 DEBUG org.apache.ranger.plugin.classloader.RangerPluginClassLoader: <== RangerPluginClassLoader.deactivate()
2021-06-26 06:51:38,420 ERROR org.apache.hadoop.crypto.key.kms.server.KMS: Exception in getkeyNames.
org.apache.hadoop.security.authorize.AuthorizationException: User:ranger not allowed to do 'GET_KEYS'
2021-06-26 06:51:38,420 WARN org.apache.hadoop.crypto.key.kms.server.KMS: User ranger (auth:PROXY) via rangeradmin/n02.py.local@PY.LOCAL (auth:KERBEROS) request GET http://n03.py.local:9292/kms/v1/keys/names?doAs=ranger caused exception.
org.apache.hadoop.security.authorize.AuthorizationException: User:ranger not allowed to do 'GET_KEYS'
2021-06-26 06:52:04,559 INFO org.apache.ranger.audit.provider.BaseAuditHandler: Audit Status Log: name=kms.async.summary.multi_dest.batch.solr, interval=01:00.003 minutes, events=1, deferredCount=1, totalEvents=3, totalDeferredCount=3
2021-06-26 06:52:04,560 INFO org.apache.ranger.audit.destination.SolrAuditDestination: Solr zkHosts=null, solrURLs=null, collectionName=ranger_audits
2021-06-26 06:52:04,560 ERROR org.apache.ranger.audit.queue.AuditFileSpool: Error sending logs to consumer. provider=kms.async.summary.multi_dest.batch, consumer=kms.async.summary.multi_dest.batch.solr
2021-06-26 06:52:04,560 INFO org.apache.ranger.audit.queue.AuditFileSpool: Destination is down. sleeping for 30000 milli seconds. indexQueue=0, queueName=kms.async.summary.multi_dest.batch, consumer=kms.async.summary.multi_dest.batch.solr
2021-06-26 06:52:04,691 INFO org.apache.ranger.audit.provider.BaseAuditHandler: Audit Status Log: name=kms.async.summary.multi_dest.batch.hdfs, interval=01:00.012 minutes, events=1, deferredCount=1, totalEvents=3, totalDeferredCount=3
Is there anything mis-configured or need to be checked? Thank you
Best Regards,
Jake Zhang
Created 06-30-2021 01:33 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
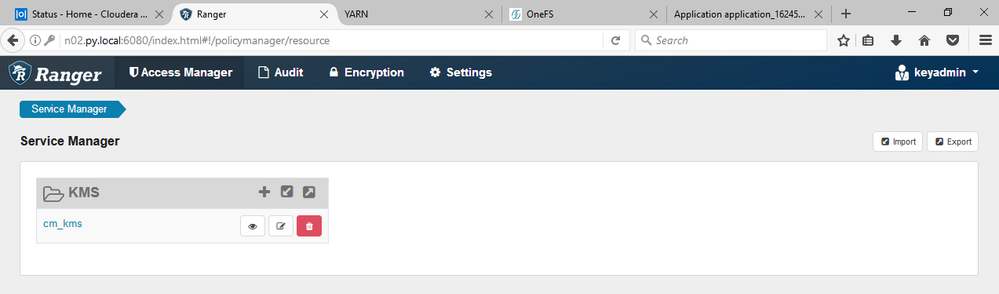
@jakezhang From the screenshot, I can see cm_kms policy is not in sync
Policy needs to be sync after ranger users is added to the policy, then only the Ranger user will be allowed to Get the keys
Created 06-26-2021 08:54 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
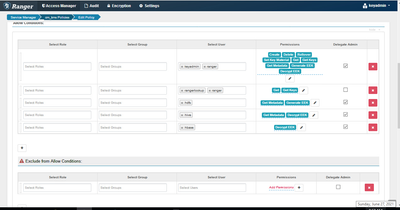
@jakezhang Assign getkeys permission for ranger user in ranger policy
Created 06-26-2021 05:59 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks.
However the permissions are already assigned in the default policy:
cm_kms
Created 06-27-2021 09:42 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jakezhang Check is cm_kms policy is in sync
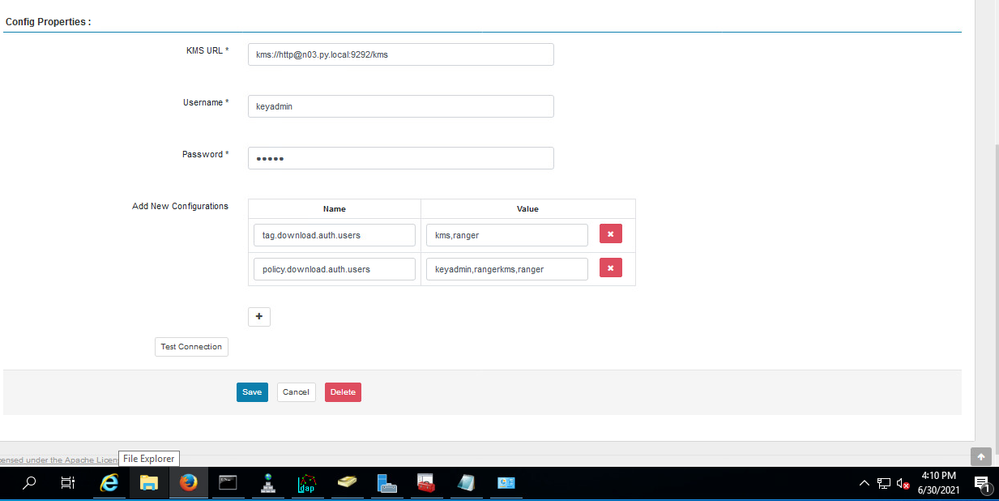
Also, modify the Config Properties values in cm_kms as shown below
tag.download.auth.users=kms
policy.download.auth.users=keyadmin,rangerkms
Created 06-29-2021 03:26 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you.
You might see they are already added in the previous screenshot.
Ranger user is added as well but it did not work.
tag.download.auth.users=kms,ranger
policy.download.auth.users=keyadmin,rangerkms,ranger
Created 06-29-2021 10:02 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
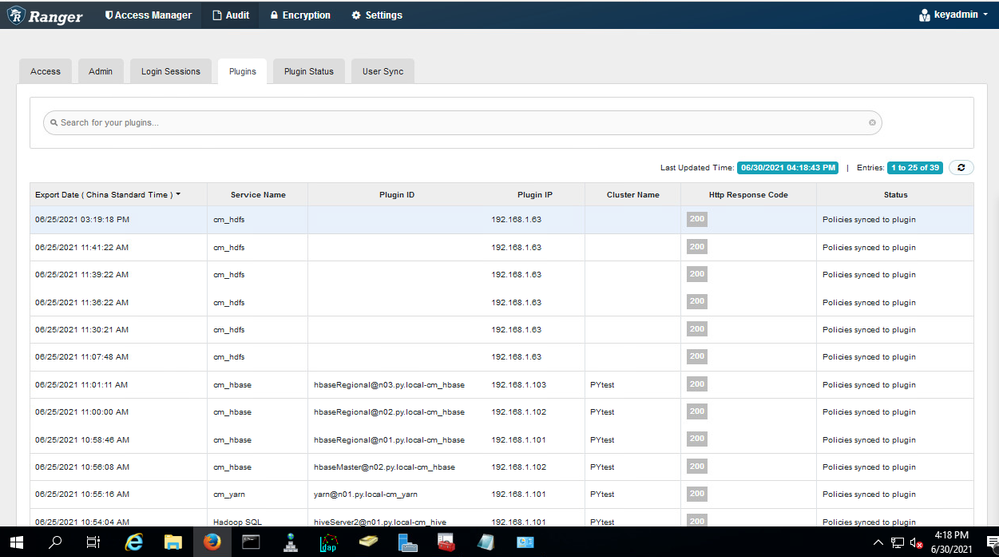
@jakezhang Can you check is cm_kms policy is in sync after adding the ranger users to the policy
Share the screenshot of Ranger Ui => Audit => Plugins
Created 06-30-2021 01:19 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Created 06-30-2021 01:33 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jakezhang From the screenshot, I can see cm_kms policy is not in sync
Policy needs to be sync after ranger users is added to the policy, then only the Ranger user will be allowed to Get the keys
Created 06-30-2021 03:05 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, but how can I get the policy synced?
Created 06-30-2021 05:51 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jakezhang Check ranger KMS logs and see what is the error while refreshing the policy