Community Articles
- Cloudera Community
- Support
- Community Articles
- Automated Kerberos Installation and Configuration
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Created on 04-23-2016 09:46 PM - edited 09-16-2022 01:34 AM
Note - I did receive few complaints about this script that it's failing on new Ambari versions, It happened because of change in kerberos payload. I have modified the script and it works like a charm again for new versions. Please continue to provide me the feedback! 🙂
Disclaimer - "Please do not use unless you know what u r doing! Test on Dev. cluster before using on production systems" 🙂
Automated Kerberos Installation and Configuration – For this post, I have written a shell script which uses Ambari APIs to configure Kerberos on HDP Single or Multinode clusters. You just need to clone our github repository and modify property file according to your cluster environment, execute setup script and phew!! Within 5-10 minutes you should have your cluster completely secured by Kerberos! Cool isn’t it?
Detailed Steps(Demo on HDP Sandbox 2.4):
1. Clone our github repository Ambari server in your HDP Cluster
Note - This script will install and configure KDC on your Ambari Server.
git clone https://github.com/crazyadmins/useful-scripts.git
Sample Output:
[root@sandbox ~]# git clone https://github.com/crazyadmins/useful-scripts.git Initialized empty Git repository in /root/useful-scripts/.git/ remote: Counting objects: 29, done. remote: Compressing objects: 100% (25/25), done. remote: Total 29 (delta 4), reused 25 (delta 3), pack-reused 0 Unpacking objects: 100% (29/29), done.2. Goto useful-scripts/ambari directory
[root@sandbox ~]# cd useful-scripts/ambari/ [root@sandbox ambari]# ls -lrt total 16 -rw-r--r-- 1 root root 5701 2016-04-23 20:33 setup_kerberos.sh -rw-r--r-- 1 root root 748 2016-04-23 20:33 README -rw-r--r-- 1 root root 366 2016-04-23 20:33 ambari.props [root@sandbox ambari]#
3. Copy setup_kerberos.sh and ambari.props to the host where you want to setup KDC Server
4. Edit and modify ambari.props file according to your cluster environment
Note - In case of multinode cluster, Please don't forget to add comma separated list of hosts as a value of KERBEROS_CLIENTS variable.
Sample output for my Sandbox
[root@sandbox ambari]# cat ambari.props CLUSTER_NAME=Sandbox AMBARI_ADMIN_USER=admin AMBARI_ADMIN_PASSWORD=admin AMBARI_HOST=sandbox.hortonworks.com KDC_HOST=sandbox.hortonworks.com REALM=HWX.COM KERBEROS_CLIENTS=sandbox.hortonworks.com ##### Notes ##### #1. KERBEROS_CLIENTS - Comma separated list of Kerberos clients in case of multinode cluster #2. Admin princial is admin/admin and password is hadoop [root@sandbox ambari]#
5. Start installation by simply executing setup_kerberos.sh
Notes:
1. Please run setup_kerberos.sh from KDC_HOST only, you don’t need to setup or configure KDC, this script will do everything for you.
2. If you are running script on Sandbox then please turn OFF maintenance mode for HDFS and turn ON maintenance mode for Zepplin Notebook before executing the script.
sh setup_kerberos.sh
Screenshots:
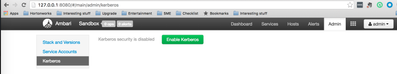
1. Before Script execution
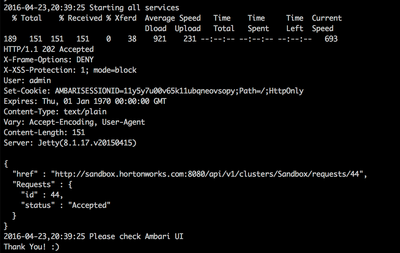
2. Script execution is in progress
3. Script execution has finished
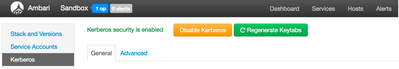
4. Voila!!
Please comment if you have any feedback/questions/suggestions. Happy Hadooping!!
Created on 04-28-2016 09:28 AM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks Kuldeep Kulkarni. This is working perfectly fine. But its not generating keytabs for root user. Which is resulting in user not found in KDC database when i am trying to run "hadoop fs -ls /" command. Is there a way to acheive this ?
Created on 05-06-2016 01:18 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you, the script works and the Kerberos is enabled after running the script.
But how to connect Toad for apache hadoop?
can you please provide the instruction?
Thanks,
Created on 05-07-2016 09:47 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
you can create your own root principal
su admin bash-4.1$ kadmin Couldn't open log file /var/log/kadmind.log: Permission denied Authenticating as principal admin/admin@HWX.COM with password. Password for admin/admin@HWX.COM: kadmin: add_principal root Enter password for principal "root@HWX.COM": Re-enter password for principal "root@HWX.COM": kadmin: exit
Created on 05-08-2016 07:42 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you @Artem Ervits & @vinay kumar
Created on 05-08-2016 07:42 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@Richard Guo - Thank you. Yes for AD, work is in progress. I will update you once done
Created on 05-09-2016 08:10 AM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
whom are you referring to by "admin" ? FYI. I am using AD as KDC. I don't have a local KDC.
Created on 05-09-2016 11:18 AM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Local user on OS
Created on 05-09-2016 03:25 PM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
How to create a keytab file to root to login remotely?
Thanks
Created on 05-13-2016 07:12 AM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks Kuldeep,
Can you suggest that how we can configure for Multi node custer?
Created on 05-22-2016 10:10 AM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@shivom mali - You can use same script, only you need to add comma separate hosts in ambari.properties for KERBEROS_CLIENTS