Community Articles
- Cloudera Community
- Support
- Community Articles
- Configuring NiFi to use LDAPS
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Created on 02-02-2017 04:34 PM - edited 08-17-2019 05:13 AM
Assumptions
The following assumptions are made. The openldap clients and server are already installed. The basic setup of the ldap server has been completed and users "nifi admin", "nifi user1" and "nifi user2" are in the ldap database.
LDAPS System Configuration
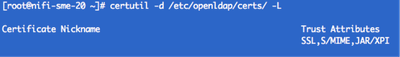
The example below is being configured on system nifi-sme-20. The CA certificate being used, aka truststore, is called, all-trusted.jks and the server certificate, aka keystore, is called nifi-sme-20.cert.pfx. There is also the encrypted private key for the server, nifi-sme-20.key.enc.pem which is needed for the configuration of the ldaps service. List the current certificates in the database, the default location is /etc/openldap/certs, using the following command:
certutil -d /etc/openldap/certs/ -L
Output will look like the following
If your CA is in pem format, then it can be imported into the NSS database. If you have a CA that is in jks format, it first must be converted before it can be imported.
Converting it can be done in two steps:
keytool -importkeystore -srckeystore all-trusted.jks -destkeystore all-trusted.p12 -deststoretype PKCS12
openssl pkcs12 -in all-trusted.p12 -out all-trusted.pem
Now the truststore can be imported into the database
certutil -d /etc/openldap/certs/ -A -n "CAcert" -t CT,, -a -i /opt/configuration-resources/certs/all-trusted.pem
This command adds a CA certificate stored in the PEM (ASCII) formatted file named /opt/configuration-resources/certs/all-trusted.pem, the -t CT,, means that the certificate is trusted to be a CA issuing certs for use in TLS clients and servers.
To verify the CA has been imported use the certutil command from above to list
Now import the server certificate in the database.
certutil -d /etc/openldap/certs/ -A -n "nifi-sme-20" -t u,u,u -a -i /opt/configuration-resources/certs/nifi-sme-20-cert.cer
This command adds the server certificate, the -t u,u,u, means the certificate can be used for authentication or signing.
Now list the contents in the database, you see the following
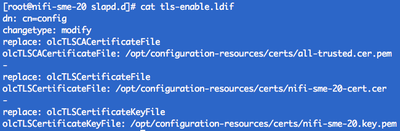
Next update the slapd service to use the CA and server certificate. This is done by updating the
/etc/openldap/slapd.d/cn=config.ldif file. The file cannot be edited manually, you have to update the file by using the ldapmodify command. One way to do this is create your own file.ldif file with the updates needed and then use this file as a parameter on the ldapmodify command. For this article, I created a file called tls-enable.ldif, here is a copy of the file:
TLSCertificateFile this directive specifies the file that contains the slapd server certificate
TLSCACertificateFile this directive specifies the PEM-format file containing certificates for the CA's that slapd will trust
TLSCertificateKeyFile this directive specifies the file that contains the private key that matches the certificate stored in the TLSCertificateFile file.
Note: To use the private key, we need to decrypt it, this can done with the following command:
openssl rsa -in nifi-sme-20.key.enc.pem -out nifi-sme-20.key.pem
The command used to update the cn=config.ldif is:
ldapmodify -Y EXTERNAL -H ldapi:/// -f tls-enable.ldif
Now restart the slapd service
systemctl status slapd
Now verify that you are able to connect to the slapd service, run the following command:
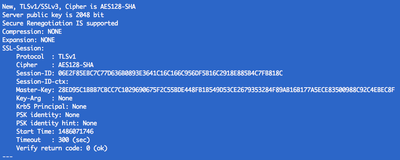
openssl s_client -connect nifi-sme-20:636 -debug -state -CAfile /opt/configuration-resources/certs/all-trusted.pem
If the commands works, output similar to this is displayed
This will put you into a shell , which you can use control-c to exit. In addition, if you check the status of the slapd service, you will also see the connection from the above command
LDAPS NiFi Configuration
Now that you have successfully configured the slapd service, there are a few steps to setup NiFi to use LDAPS.
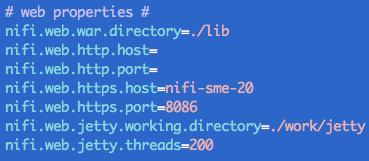
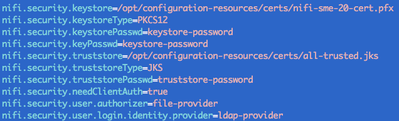
First, configure NiFi to perform user authentication over HTTPS, the following sections in the nifi.properties file section need to be completed. Again for this example, the configuration is being done on system nifi-sme-20.
Make sure to set the web section to use https host and port
In addition, fill in the security section with the keystore and truststore. In this example, I use the same CA certificate in the nifi.properties as the ldaps service, but it isn't a requirement for it to work with NiFi. The CA used in the configuration of the login-identity-provider.xml has to be the same as the one used in the configuration of the ldaps service.
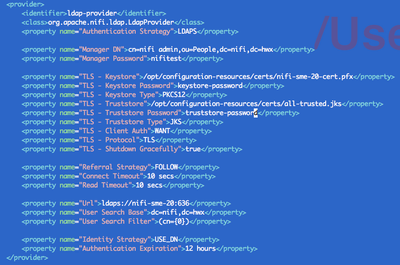
Notice also that the nifi.security.user.login.identity.provider is set to ldap-provider. Now edit the login-identity-provider.xml file and add the keystore, truststore and all of the other TLS properties. Once you set the authentication strategy to LDAPS, all of the other properties are required to have some value. Inside the file is short explanation of each property and the possible values.
If this is the first time to secure the NiFi instance, the last step is to set the initial admin identity in the authorizers.xml file.
Now restart/start NiFi.
This is what you will see when you go to the NiFi UI in the browser:
And there you go, you have successfully configured NiFi to use LDAPS.